Safeguard Your Properties with BQT Electronic Safety Systems
Safeguard Your Properties with BQT Electronic Safety Systems
Blog Article
Maximizing Service Protection: The Ultimate Overview to Electronic Protection Solutions
In the fast-paced and ever-evolving landscape of company safety and security, the dependence on digital safety and security options has become paramount for securing valuable possessions, secret information, and keeping functional connection. As risks to organizations proceed to grow in intricacy and frequency, the need for a thorough and durable safety approach can not be understated. In this overview to digital security options, we will certainly explore the most recent fads, cutting-edge technologies, and finest methods to fortify your service versus possible risks and vulnerabilities. Stay ahead of the contour and guarantee the protection of your company with our in-depth assessment of electronic security solutions.
Importance of Electronic Safety Solutions
When taking into consideration the security of properties and sensitive information, the relevance of electronic safety options can not be overemphasized. In today's interconnected world, where cyber dangers are regularly advancing and ending up being a lot more advanced, companies have to focus on carrying out robust digital protection steps to protect their data and procedures. Electronic security services incorporate a wide variety of technologies and methods developed to resist unapproved access, information breaches, malware, and various other cyber hazards.
One of the key advantages of electronic protection services is their ability to supply real-time monitoring and threat detection. BQT Biometrics Australia. With tools like breach discovery systems, firewalls, and protection details and event management (SIEM) systems, organizations can proactively identify and react to protection events prior to they intensify right into significant violations. Furthermore, electronic security solutions assist make sure conformity with sector regulations and requirements, protecting organizations from prospective lawful and financial effects
Kinds of Electronic Safety And Security Equipments
Provided the vital significance of electronic protection options in safeguarding businesses versus cyber dangers, it is important to explore the numerous sorts of digital security systems readily available to enhance defense and resilience. Among one of the most typical sorts of electronic protection systems is the firewall, which functions as an obstacle between a business's interior network and exterior networks, removing possibly unsafe information. Intrusion Detection Equipment (IDS) are additionally important, as they check network traffic for dubious task and sharp administrators to prospective hazards. Furthermore, services commonly count on file encryption modern technologies to protect delicate data both at remainder and in transit. Accessibility control systems, including biometric readers and keycard gain access to, assistance regulate access to physical rooms and safeguard assets. Video clip security systems play a role in tracking and recording activities within and around the premises. By using a mix of these electronic safety systems, organizations can establish a durable defense against different protection risks.
Applying Gain Access To Control Actions

In addition, accessibility control procedures can be incorporated with security systems to keep an eye on and record individuals' movements within safeguarded areas. This combination enhances safety and security by giving a thorough overview of that is accessing certain places at any type of provided time. Accessibility control systems can be configured to restrict accessibility based on time, area, or individual qualifications, enabling organizations to tailor protection protocols according to their details demands.
Cybersecurity Ideal Practices
To improve general safety position, implementing durable cybersecurity ideal practices is necessary in safeguarding electronic properties and data integrity. Carrying out routine safety audits and assessments aids determine weaknesses and locations for renovation.
Establishing a thorough event response plan makes it possible for swift and efficient responses to security breaches, lessening prospective damages. Encrypting delicate information both in transit and at remainder supplies an additional obstacle against information breaches. Implementing access controls based upon the concept of least privilege restricts the direct exposure of crucial systems and information to just those that need it for their functions. Normal back-ups of information ensure that in the occasion of a ransomware attack or go to these guys information loss, critical information can be recouped. Welcoming an aggressive method to cybersecurity with continuous monitoring This Site and hazard intelligence aids spot and minimize potential dangers prior to they intensify. By including these best techniques into cybersecurity methods, services can fortify their defenses versus developing cyber hazards.
Security and Surveillance Solutions
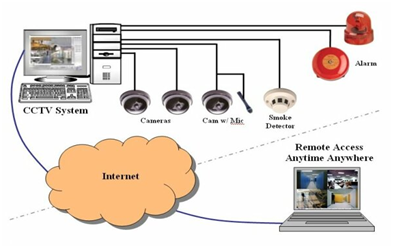
Video clip surveillance services offer remote tracking capabilities, permitting licensed personnel to maintain an eye on the properties even when off-site. Furthermore, advanced attributes like activity detection, facial recognition, and permit plate recognition enhance the overall security position of the organization. Integrating security systems with alarm and access control even more reinforces the protection facilities, making it possible for an aggressive action to prospective safety and security breaches.
Final Thought
To conclude, digital security options are important for optimizing organization defense. By applying accessibility control measures, cybersecurity ideal practices, and monitoring and tracking options, businesses can successfully secure their possessions and information. It is essential to spend in the right electronic safety and security systems to make sure the safety and security of the organization. Remember, avoidance is key in safeguarding YOURURL.com versus potential threats and vulnerabilities (BQT Solutions).
Report this page